The Fallon Post
EVENTS!
Pressure: 1010 hPa
Wind: 13 mph
COMMENTS
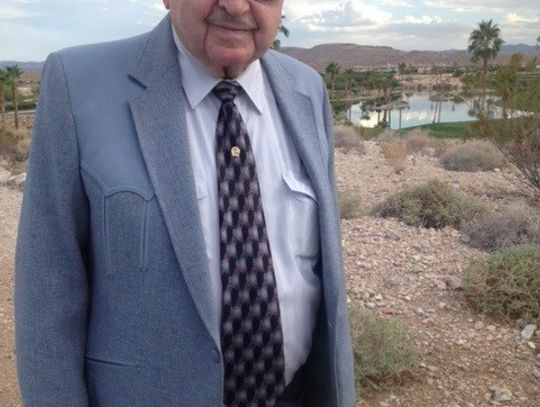
Comment author: Claude EzzellComment text: Paul was one of the most manifest men I have ever met. He was a good friends with my Dad and always had an entertaining story for the occasion. One of my most favorite stories Paul told dated back to the late 60s or early 70s and it revolved around him killing a deer way out in the mountains. Naturally the deer ran down into a deep canyon and died. Knowing that it would take him forever to haul it out he devised an awesome plan. After preparing the deer he drove back to NAS Fallon and rustled up a SAR crew and they flew out and picked up the deer. Of course it was labeled as a training flight but what the hell in those days you could do that sort of thing. Rest in Peace my friend until we meet again!!Comment publication date: 4/11/24, 1:15 PMComment source: Obituary - LCDR Paul N PflimlinComment author: THughesComment text: So sad to hear. Prayers to the Goings family.Comment publication date: 4/5/24, 6:35 PMComment source: Obituary - Bill GoingsComment author: April SmithComment text: I love this beautiful woman and her family so much. Such a pure soul and I had a great pleasure taking care of her while she was at the homestead and being by her side for her last daysComment publication date: 4/2/24, 8:50 PMComment source: Obituary - Frances Elaine (Sanford) Atkinson